EU NIS2 Directive: Prepare to meet the new requirements
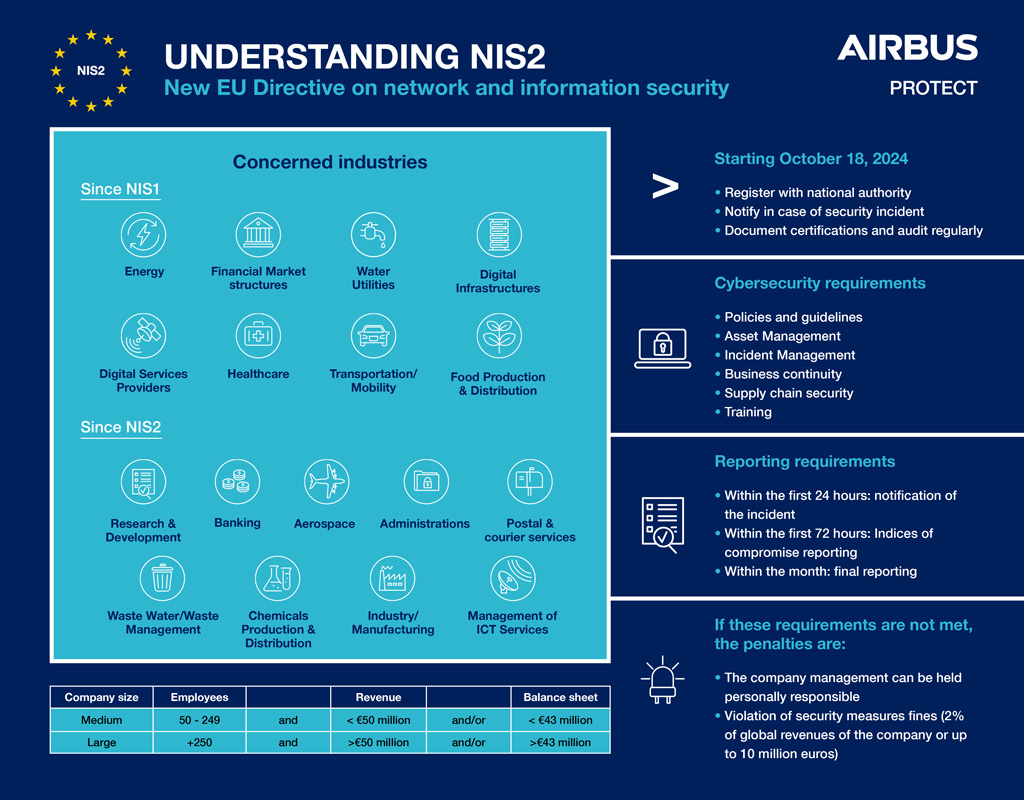
With the NIS2 Directive, mandatory security measures and reporting obligations will apply to many companies from October 2024 – even those not previously affected.
The NIS2 Directive (Network and Information Systems 2 Directive) is a comprehensive piece of EU legislation designed to enhance cybersecurity across member states. The directive aims to strengthen the resilience of critical infrastructure and services against cyber threats and reduce the impact of security incidents.
From October 2024, it will replace the original 2016 NIS Directive, which had been the first legislation aimed at improving the cybersecurity posture of the EU. The NIS2 Directive revises and extends the previous legislation to address the rapid evolution of the threat landscape, reflecting the growing sophistication of cyberattacks and the increasing interdependencies between sectors.
NIS2 establishes common rules for cybersecurity across various sectors and introduces more robust security requirements expanding the scope of application to more critical sectors, such as energy, transport, banking, and healthcare. In particular, digital service providers and platforms are now also included in the scope of NIS2, which significantly extends the reach of the directive.
Differences between NIS2 and the first NIS Directive
Adopted in July 2016, the NIS1 Directive (Network and Information Security) was the European Union’s first legislative response to the escalating wave of cyber threats. As a groundbreaking legal instrument, its aim was to establish a common level of cybersecurity across member states’ networks and information systems. It was crafted in a context of increasing digital dependency, where the compromise of critical infrastructure could have severe consequences on security, the economy, or even public health.
NIS1 applied mainly to operators of essential services (OES) and digital service providers (DSPs). Targeted sectors included energy, transport, health, digital infrastructure, and finance.
One of NIS1’s key contributions was the creation of a cooperation framework between EU countries facilitating information-sharing and best practices and fostering coordinated and effective responses to cross-border cyber incidents.
Despite its achievements, NIS1’s implementation revealed several shortcomings:
- Member States transposed the directive with varying approaches, resulting in a lack of harmonization.
- The criteria for identifying OES were sometimes inconsistent, leading to disparate applications across countries.
- Key actors in the digital supply chain were often left outside its scope.
- Minimum sanctions were left to national discretion, thereby limiting the directive’s deterrent effect.
- The rise of new threat vectors quickly highlighted the need for a stronger legal framework.
This is where NIS2 comes in: designed to address NIS1’s limitations, it significantly expands the scope of entities concerned, introduces a more consistent approach across Member States, and enforces stricter oversight mechanisms with clearly defined sanctions. The transition from NIS1 to NIS2 marks a major step toward a more robust European cybersecurity posture, aligned with today’s digital realities.
Is your company affected by the NIS2 Directive?
Check whether you will be affected and which requirements you need to fulfil:
– Risk analysis and security policies for information systems
– Incident handling
– Business continuity management
– Backup management
– Crisis management
– Supply chain security
– Security measures for the acquisition, development, and maintenance of network and
information systems
– Vulnerability management
– Evaluation of the effectiveness of risk management measures
– Security procedures for employees with access to sensitive or important data
– Cybersecurity training and awareness
– Concepts for the use of cryptography
– Access control and asset management
– Use of multi-factor authentication (MFA) or continuous authentication (SSO)
– Secured voice, video, and text communication and, if necessary, secure emergency
communication systems
– Implementation of an information security management system
To get an overview of all topics, you can download our NIS2 checklist.
What are the requirements of the NIS2 Directive?
Organisations subject to the NIS2 Directive must meet several key requirements to ensure compliance:
Cybersecurity Risk Management and Mitigation
- Conduct risk assessments to identify threats and vulnerabilities.
- Implement incident detection and response systems to mitigate risks.
- Develop business continuity and contingency planning to minimise disruption.
NIS2 mandates minimum security measures, including encryption, multi-factor authentication, and employee cybersecurity training.
Incident Reporting
- Prompt reporting of significant incidents to national authorities, detailing the incident’s nature, systems affected, and mitigation steps.
- NIS2 requires 24-hour early warning for high-risk incidents, ensuring swift response and stakeholder communication.
Supply Chain Security
- Ensure that suppliers and contractors follow similar cybersecurity standards.
- Emphasise supply chain risk management to prevent vulnerabilities from spreading through third parties.
Governance, Risk and Compliance
- Appoint a designated senior individual responsible for cybersecurity.
- Maintain strong corporate accountability and governance frameworks to continuously monitor and improve cybersecurity practices.
Auditing and Regular Testing
- Regularly test cybersecurity defenses and conduct vulnerability assessments.
- Ensure continuous system monitoring to identify and address emerging threats.
Reporting obligations for cyber incidents: What should you report?
It’s crucial to know which cyber incidents need to be reported, to whom, and in what timeframe. For example, an initial early warning must be sent to the country-specific security authority within 24 hours of a suspected incident. If the suspicion is substantiated or confirmed, a report on the security incident must follow within 72 hours. Lastly, a final report must be sent no later than one month after notification of the confirmed incident.
The final report must include the following:
- Incident response report
- Discussion of the exploited vulnerability
- Remedial measures taken and ongoing
- Area of impact
- If the incident is not resolved within a month, organisations are required to deliver a progress report instead. In this case, the final report should follow no later than one month after the security incident has been dealt with.
As you can see, these deadlines are extremely tight. To save valuable time in the event of an incident, we recommend an annual ‘incident response emergency drill’ and a framework contract for incident response activities. This enables the response team to familiarise themselves with your systems in ‘peacetime’. It also allows you to define contact people, crisis teams and decision-makers in advance and familiarise them with important processes in the communication chain.
What are the penalties for non-compliance with the Nis2 Directive?
Failure to comply with the NIS2 Directive can lead to severe consequences for organisations, including:
Financial Penalties
Non-compliance can result in substantial fines and penalties, which can be a significant financial burden, particularly for smaller organisations.
The directive sets out financial penalties that vary depending on whether an organisation is classified as an “essential” or “important” entity.
For essential entities, the penalties can go up to €10 million or 2% of global annual revenue, whichever is greater. For important entities, financial penalties can reach up to €7 million or 1.4% of global annual turnover, whichever is higher.
Legal Liabilities
If organisations fail to comply with the NIS2 Directive, they may be held legally liable for any damage caused by security breaches, particularly if these breaches affect critical national infrastructure.
Operational Disruptions
Cyberattacks can cause significant operational disruptions. Without proper risk management and incident response plans, organisations could face prolonged downtime, data loss, or service outages.
Reputation Damage
Organisations that fail to meet cybersecurity standards risk damaging their reputation. Data breaches and cyberattacks can lead to loss of customer trust and harm business relationships.
How to prepare for NIS2?
-
Determine Coverage
First, confirm whether your company falls under the scope of NIS2. If your company operates in critical sectors, perform a gap analysis to identify differences from the previous NIS Directive, especially if you were already covered under NIS1.
-
Identify Critical Processe
Conduct a Business Impact Assessment to identify essential services, processes, and assets that are crucial for your operations and their reliance on network and information systems. This assessment will help define the scope of your compliance efforts.
-
Implement a Risk Management System
Set up a risk and information security management system to identify, treat, and monitor cybersecurity risks. Ensure this system covers key areas such as risk management policies, incident handling, business continuity, supply chain security, and employee training.
-
IT Supply Chain Security
Review and strengthen the security of your IT supply chain, especially focusing on critical suppliers. Address any security gaps and vulnerabilities in contracts or technical operations.
-
Create an Implementation and Maintenance Plan
Develop a clear implementation and maintenance plan that includes deadlines for addressing security gaps. You should be able to show authorities that cybersecurity is being continuously monitored and improved.
-
Implement Security Measures
Start implementing the necessary security measures based on your risk assessments. Adopting frameworks like ISO 27001 or following CIS Critical Security Controls can help ensure your company is meeting the requirements of NIS2.
-
Establish a Cyber-Oriented Culture
Promote a culture of cybersecurity across the organisation. Employees should be trained to understand their role in maintaining cybersecurity, and management must prioritise cybersecurity as essential to the company’s survival.
Not sure what to do next? Our experienced consultants can help you.
The directive is extensive, with many considerations and possible solutions. Airbus Protect has a team of experts who can support you to make NIS2 compliance less of a headache.
Our experts use purpose-built methodologies and frameworks and tailor our services to your needs. These include:
- Inventory
- NIS2 audit and gap analysis
- Advice on cost-effective solutions
- Planning and organisation of the next steps
- Support with implementation
- Ongoing support and optimisation
Do you need support in implementing the NIS2 directive? We’d be happy to help you.
Want to learn more about our Governance, Risks, Compliance & Audit services?